I have been running dual DNS servers on my home network for a while, see my previous post about setting them up: Debian Server on a Thin Client with a Flash Drive
The inevitable finally happened–after a year of faithful service (and years past its expected life), my primary server (the DevonIT box) finally died. I traced it down to a couple of blown capacitors in the power supply, and while I am perfectly capable of replacing them, I decided to use the opportunity to put my Christmas present to good use.
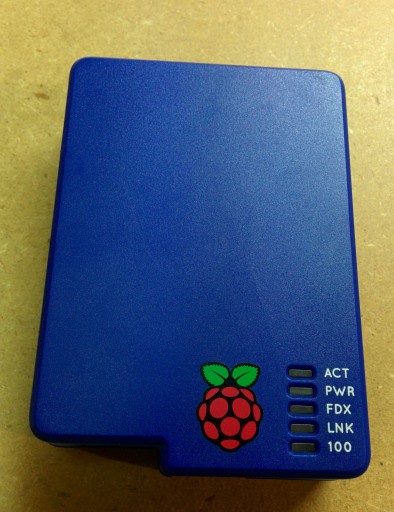
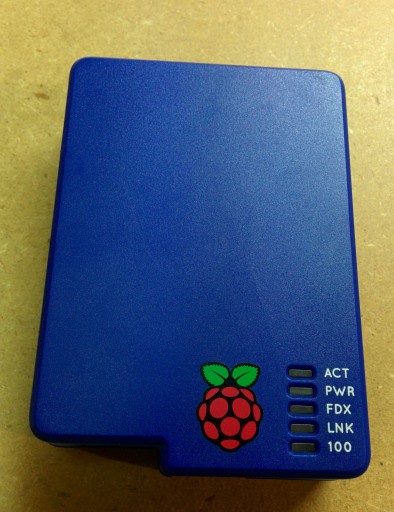
I decided that if my Raspberry was going to find permanent usage in my stack of equipment it needed a real case on it to protect from electrical shorts and other damage. Why I choose the “blueberry” case for the Raspberry, I can’t explain, I guess I just like the look.
I first attempted to get this running on an 8GB Class 2 SD I stole from my wife’s camera. While it was technically functional, it was vvveeerrryyy ssslllooowww, convincing me I needed a proper card like this:

Panasonic Gold Series 8GB Class 10 SDHC Memory Card
http://www.adorama.com/PCSDUB08GAK.html
I also needed a good power supply. The Pi takes about 500-700 mA by itself, significantly more if you plug in a USB stick or WiFi adapter (potentially 500 mA each). I found most typical cell chargers run in to 500 mA-1 A range. I ended using a 1 A charger I had lying around, but I’d recommend something like this:

USA Raspberry Pi Micro USB Power Supply Charger – 5v 1500ma
Alternatively, if you plan to have several devices you’re probably better off with a multi-port charger that can safely supply enough juice:
One word of caution–make sure the charger/power supply is UL listed (or certified by an equivalent regulatory body) . As my father (the electrical inspector) reminded me, if you’re going to run this 24×7 with cables all tucked in a dark corner, the last thing you want to stress about is everything going up in flames because you saved a few dollars buying a cheap charged from Asia.
I went with the standard Raspbian distro downloaded from official sources (http://www.raspberrypi.org/downloads/). The advantage of this is a simple, easy to install distro that is optimized for the Pi, yet resembles standard Debian as closely as possible. The main disadvantage is that it comes loaded with junk not required/desired on a small, headless server. I followed the instructions on this thread to clean up unwanted packages:
http://raspberrypi.stackexchange.com/questions/4745/how-to-uninstall-x-server-and-desktop-manager-when-running-as-headless-server
As of now, I’m down to 800MB of disk space used, and I’m not done yet.
Tasks left to be completed:
- Continue to search out and remove undesired packages
- Follow Linux hardening guidelines to make the system more secure
- Set up remote logging — I have an internal syslog server, but I’m considering trying out https://papertrailapp.com/
Being a busy guy, this posting isn’t nearly as complete and polished as I’d like it to be, but hopefully someone will find it useful.
Posted: October 11th, 2014 under Linux.
Comments: none